Binance Security Report: Deployed hundreds of AI models for defense system, cumulatively intercepted $10.53 billion in risky funds
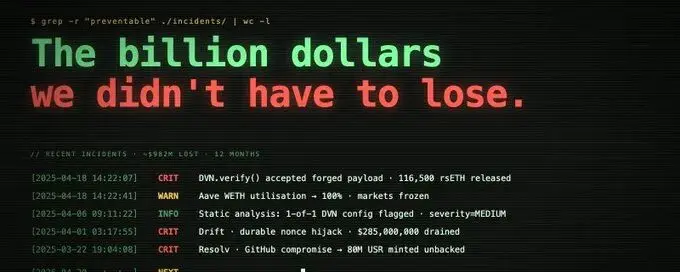
Binance released its latest security report, addressing the current industry situation of rapidly spreading AI scams. The platform has deployed over 24 AI security programs and equipped more than 100 AI models to build an intelligent defense system against various types of cryptocurrency fraud.Statistics show that from early 2025 to the first quarter of 2026, Binance has protected over 5.4 million users and intercepted potential fund losses of $10.53 billion. In Q1 2026, the platform successfully intercepted 22.9 million scam and phishing attacks, protecting user funds amounting to $1.98 billion, with an average of over 9,600 real-time risk alerts pushed daily, and a total of 36,000 malicious on-chain addresses blacklisted.The report pointed out that deepfakes, voice cloning, and phishing bots have become mainstream scam tactics, with the overall scale of cryptocurrency fraud reaching $17 billion in 2025, a year-on-year increase of 30%. In terms of risk control, Binance's AI system handles 57% of fraud detection work, reducing the credit card fraud rate to 60%-70% of the industry average; it has upgraded AI anti-counterfeiting KYC reviews, with review efficiency improved by up to 100 times.The AI trading tool Binance Ai Pro uses an isolated account structure, only allowing trading permissions and prohibiting withdrawals, with the platform intercepting 12% of high-risk third-party AI plugins. Additionally, in 2025, Binance assisted in recovering $12.8 million in scammed funds, handled 48,000 cases, and collaborated with law enforcement to freeze $131 million in illegal assets.
 BTC $79,086.74 -2.81%
BTC $79,086.74 -2.81% ETH $2,223.31 -3.29%
ETH $2,223.31 -3.29% BNB $673.10 -1.15%
BNB $673.10 -1.15% XRP $1.43 -7.00%
XRP $1.43 -7.00% SOL $89.53 -4.12%
SOL $89.53 -4.12% TRX $0.3519 -0.75%
TRX $0.3519 -0.75% DOGE $0.1130 -2.86%
DOGE $0.1130 -2.86% ADA $0.2609 -5.28%
ADA $0.2609 -5.28% BCH $426.07 -2.77%
BCH $426.07 -2.77% LINK $10.07 -5.68%
LINK $10.07 -5.68% HYPE $44.82 +1.00%
HYPE $44.82 +1.00% AAVE $93.10 -6.87%
AAVE $93.10 -6.87% SUI $1.10 -9.07%
SUI $1.10 -9.07% XLM $0.1545 -6.75%
XLM $0.1545 -6.75% ZEC $522.37 -1.97%
ZEC $522.37 -1.97% BTC $79,086.74 -2.81%
BTC $79,086.74 -2.81% ETH $2,223.31 -3.29%
ETH $2,223.31 -3.29% BNB $673.10 -1.15%
BNB $673.10 -1.15% XRP $1.43 -7.00%
XRP $1.43 -7.00% SOL $89.53 -4.12%
SOL $89.53 -4.12% TRX $0.3519 -0.75%
TRX $0.3519 -0.75% DOGE $0.1130 -2.86%
DOGE $0.1130 -2.86% ADA $0.2609 -5.28%
ADA $0.2609 -5.28% BCH $426.07 -2.77%
BCH $426.07 -2.77% LINK $10.07 -5.68%
LINK $10.07 -5.68% HYPE $44.82 +1.00%
HYPE $44.82 +1.00% AAVE $93.10 -6.87%
AAVE $93.10 -6.87% SUI $1.10 -9.07%
SUI $1.10 -9.07% XLM $0.1545 -6.75%
XLM $0.1545 -6.75% ZEC $522.37 -1.97%
ZEC $522.37 -1.97%